
Everything about Machine Learning for Cybersecurity and in-between.
There is a considerable number of articles covering machine learning for cybersecurity and the ability to protect us from cyberattacks. Still, it’s important to emphasize how actually Artificial Intelligence (AI), Machine Learning (ML),and Deep Learning (DL) can help in cybersecurity right now, and what this hype is all about.
First of all, I have to disappoint you. Unfortunately, machine learning will never be the lightning in the bottle for cybersecurity compared to image recognition or natural language processing — two areas where machine learning is thriving. There will always be a man trying to find weaknesses in systems or ML algorithms and to bypass security mechanisms. What’s worse, now hackers are able to use machine learning to carry out all their nefarious endeavors. Nowadays you don’t even need a hacker to hack things. Wild.
Not even Artificial Intelligence is immune to cyberattacks. Check out this incredibly in-depth paper published on Harvard Kennedy School’s website.
Fortunately, machine learning can aid in solving the most common tasks including regression, prediction, and classification. In the era of extremely large amount of data and cybersecurity talent shortage, ML seems to be an only solution.
This article is an introduction written to give practical technical understanding of the directions of ML research applied to cybersecurity.
Let’s understand some basic terminology.
The lingo
Stop calling everything AI. It’s not.
There’s 3 terms I would like to define and clarify. Artificial Intelligence (AI), Machine Learning (ML) & Deep Learning (DL).
- Artificial Intelligence (AI) — A vast concept. Also referred to as machine intelligence, is a branch of computer science that focuses on building and managing technology that can learn to autonomously make decisions and carry out actions on behalf of a human being. It can also be called the science of making things smart.
- Machine Learning (ML) — An approach. It is the field of study that gives computers the capability to learn without being explicitly programmed. ML is one of the most exciting technologies that one would have ever come across. As it is evident from the name, it gives the computer that makes it more similar to humans: The ability to learn. Machine learning is actively being used today, perhaps in many more places than one would expect.
- Deep Learning (DL) — a set of Techniques for implementing machine learning that recognize patterns of patterns - like image recognition. The systems identify primarily object edges, a structure, an object type, and then an object itself. The point is that Deep Learning is not exactly Deep Neural Networks.
machine learning can be broadly classified into two classes, known as supervised and unsupervised learning.
- Supervised — Where a computer algorithm is trained on input data that has been labeled for a particular output. The model is trained until it can detect the underlying patterns and relationships between the input data and the output labels, enabling it to yield accurate labeling results when presented with never-before-seen data.
- Unsupervised — Data Driven approach. The approach can be used when there are no labelled data and the model should somehow mark it by itself based on the properties. Usually it is intended to find anomalies in data and considered to be more powerful in general as it’s almost impossible to mark all data.
While there exist many other methods, we will not go too in-depth about them. For those curious, check out this article here.
Applications of Machine Learning in Cyber Security
To better understand previous cyber-attacks, and develop respective defence responses, ML can be deployed in various domains within Cyber Security to enhance security processes, and make it easier for security analysts to quickly identify, prioritise, deal with and remediate new attacks.
With machine learning, cybersecurity systems can analyze patterns and learn from them to help prevent similar attacks and respond to changing behavior. It can help cybersecurity teams be more proactive in preventing threats and responding to active attacks in real time. It can reduce the amount of time spent on routine tasks and enable organizations to use their resources more strategically.
In short, machine learning can make cybersecurity simpler, more proactive, less expensive and far more effective. But it can only do those things if the underlying data that supports the machine learning provides the complete picture of the environment. As they say, garbage in, garbage out.
Let’s discuss a few examples of the same.
Threat identification
if a hacker manages to enter their systems, they are toast! The most difficult component of cybersecurity is finding out if the connection requests into the system are legitimate and any suspicious looking activities such as receiving and sending large amounts of data are the work of employees in the company or some cyber threats.
This is very difficult to identify for cybersecurity professionals, especially in large companies and humans are not always accurate. That’s where machine learning comes in to save the day. A cyber threat identification system that is powered by AI and ML can be used to monitor all outgoing and incoming requests to the system to monitor suspicious activity. For example Versive provides AI/ML tools for the same.
Email Monitoring
It is very important to monitor the official Email accounts of employees in a company to prevent cybersecurity attacks such as phishing. Learn more about phishing in my post about Social Engineering.
Cybersecurity software along with machine learning can be used to avoid these phishing traps by monitoring the employees’ professional emails to check if any features indicate a cybersecurity threat. Natural language processing coupled with the same can make it even more efficient and accurate.
For example, Tessian is a famous software company that provides Email monitoring software that can be used to check if an email is a phishing attempt or a data breach.
AI Threats
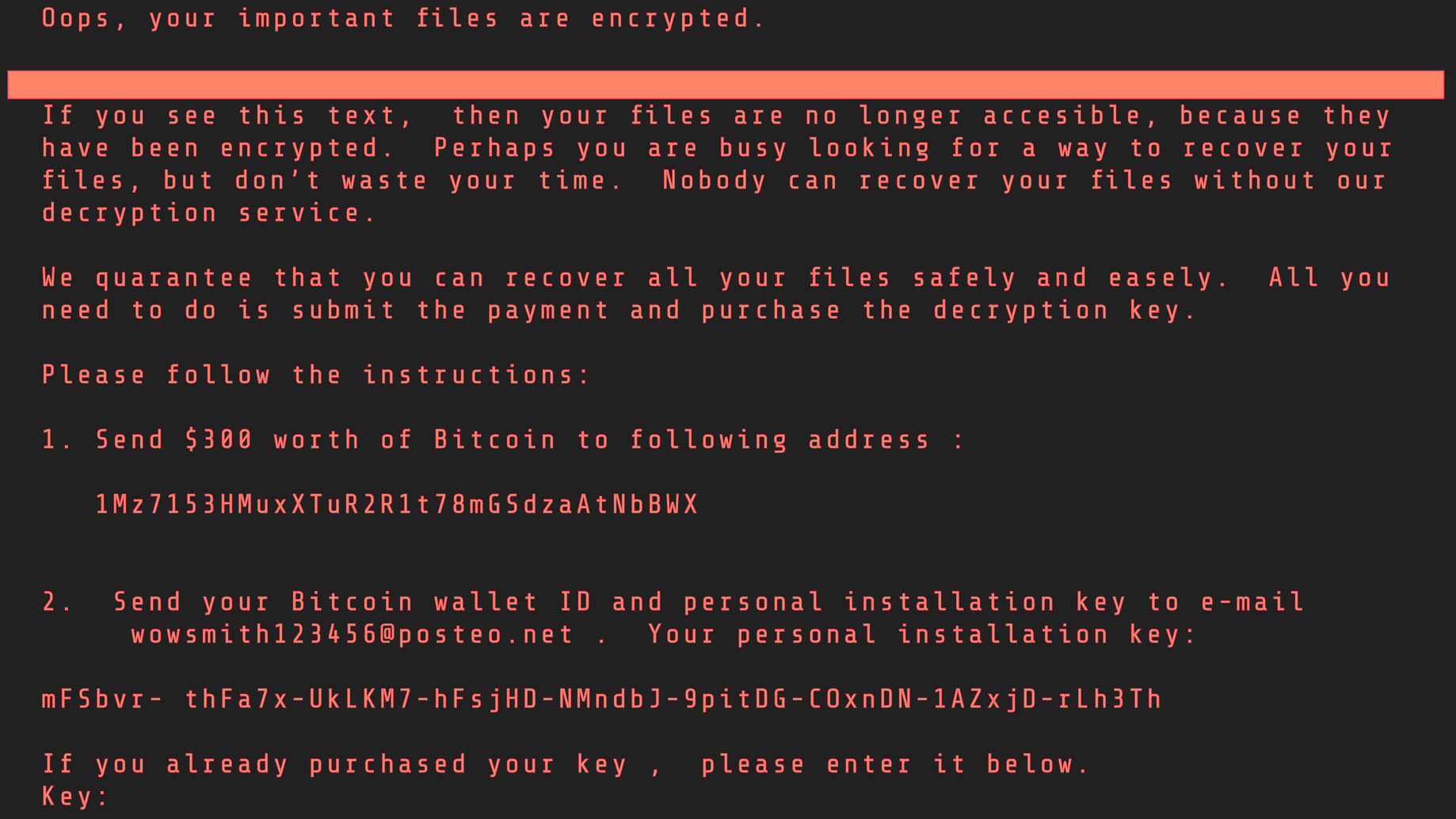
Yes. The same way AI can play defence, it can play attack. Many hackers are now taking advantage of technology and using machine learning to find the holes in security and hack systems. Therefore, it is very important that companies fight fire with fire and use machine learning for cybersecurity as well. Take into account the NotPetya attack, sometimes regarded as history’s most devastating cyberattack, utilized EternalBlue, a software hole in Microsoft’s Windows OS.
These types of attacks can get even more devastating in the future with the help of artificial intelligence and machine learning unless cybersecurity software also uses the same technology. An example of this is Crowdstrike, a cybersecurity technology company that uses Falcon Platform which is a security software embedded with artificial intelligence to handle various cyberattacks.
What lies in the future for AI/ML in Cybersecurity?
Artificial intelligence in cybersecurity is by no means perfect yet, but cybercriminals are already using automation and machine learning in their countless attacks. In this never-ending cat-and-mouse game, AI is slated to continue gaining ground to build predictive capabilities and strengthen defenses for the foreseeable future.
Machine learning will be neither predominantly offense-biased nor defense-biased, it may subtly alter the threat landscape by making certain types of strategies more appealing to attackers or defenders.
For more information and knowledge, refer to the incredibly detailed report titled “Machine Learning and Cybersecurity — Hype and Reality” on Centre for Security and Emerging Technology’s website.
//
Start blogging about your favorite technologies, reach more readers and earn rewards!
Join other developers and claim your FAUN account now!
User Popularity
34
Influence
2k
Total Hits
2
Posts
















Only registered users can post comments. Please, login or signup.