Amazon EKS Enables Ultra-Scale AI/ML Workloads with Support for 100K Nodes per Cluster
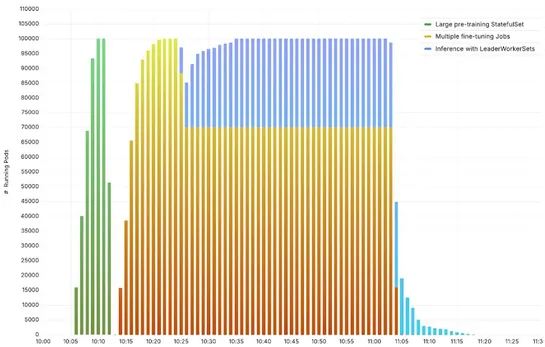
Amazon EKS just cranked its Kubernetes cluster limit to100,000 nodes—a 10x jump. The secret sauce? A reworkedetcdwith an internaljournalsystem andin-memorystorage. Toss in tightAPI server tuningand network tweaks, and the result is wild: 500 pods per second, 900K pods, 10M+ objects, no sweat—even un.. read more