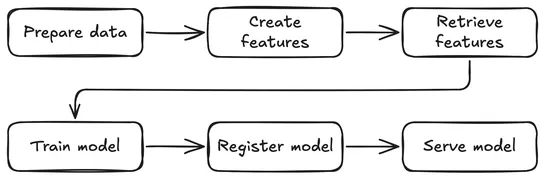
From Raw Data to Model Serving: A Blueprint for the AI/ML Lifecycle with
Post maps out aKubeflow Pipelinesworkflow onSpark,Feast, andKServe. It tackles fraud detection end-to-end: data prep, feature store, live inference. It turns infra into code, ensures feature parity in train and serve, and registers ONNX models in theKubeflow Model Registry... read more