
If you ever wondered how to save the secrets of HashiCorp's Vault with Jenkins on a daily basis, you can read it in my blog post
I am a DevOps engineer at Cloudify.co and I will share in this post my experience related to automation of Vault backup creation using Jenkins scheduled job and simple python script which I built to create dump of vault secrets.
Let’s start.
What is HashiCorp’s Vault?
Vault is a tool for securely accessing secrets. A secret is anything that you want to tightly control access to, such as API keys, passwords, certificates, and more. Vault provides a unified interface to any secret while providing tight access control and recording a detailed audit log.
https://www.vaultproject.io/
What is Jenkins Pipeline?
Jenkins Pipeline (or simply “Pipeline” with a capital “P”) is a suite of plugins that supports implementing and integrating continuous delivery pipelines into Jenkins.
https://www.jenkins.io/doc/book/pipeline/
Prerequisites:
- Vault Installed
- Jenkins Installed
My Setup
- EKS Kubernetes cluster
- Vault runs on EKS cluster
- Jenkins runs on EKS cluster
You can read in this tutorial how to run Jenkins on EKS cluster:
https://igorzhivilo.com/jenkins/ci-cd-future-k8s-jenkins/
What you will learn from this post?
- How to use python hvac library for authentication with Vault programmatically and backup vault secrets.
- What is AppRole authentication mechanism in Vault and how to enable/create it?
- How to create a scheduled backup for Vault secrets with Jenkins pipeline on k8s.
AppRole authentication method in Vault
How can an application programmatically request a token so that it can read secrets from Vault?
Using the AppRole which is an authentication mechanism within Vault to allow machines or apps to acquire a token to interact with Vault and using the policies you can set access limitations for your app.
It uses RoleID and SecretID for login.
Create AppRole and policy for Jenkins
I explained how to do it in detail in my blog post: https://igorzhivilo.com/jenkins/how-to-read-vault-secrets-from-declarative-pipeline/
After you applied everything I wrote in this post:
- enabled approle in vault
- v2 kv secrets engine enabled
- applied all needed policies
eventually you will get role_id and secret_id which will be used programmatically with ‘python hvac’.
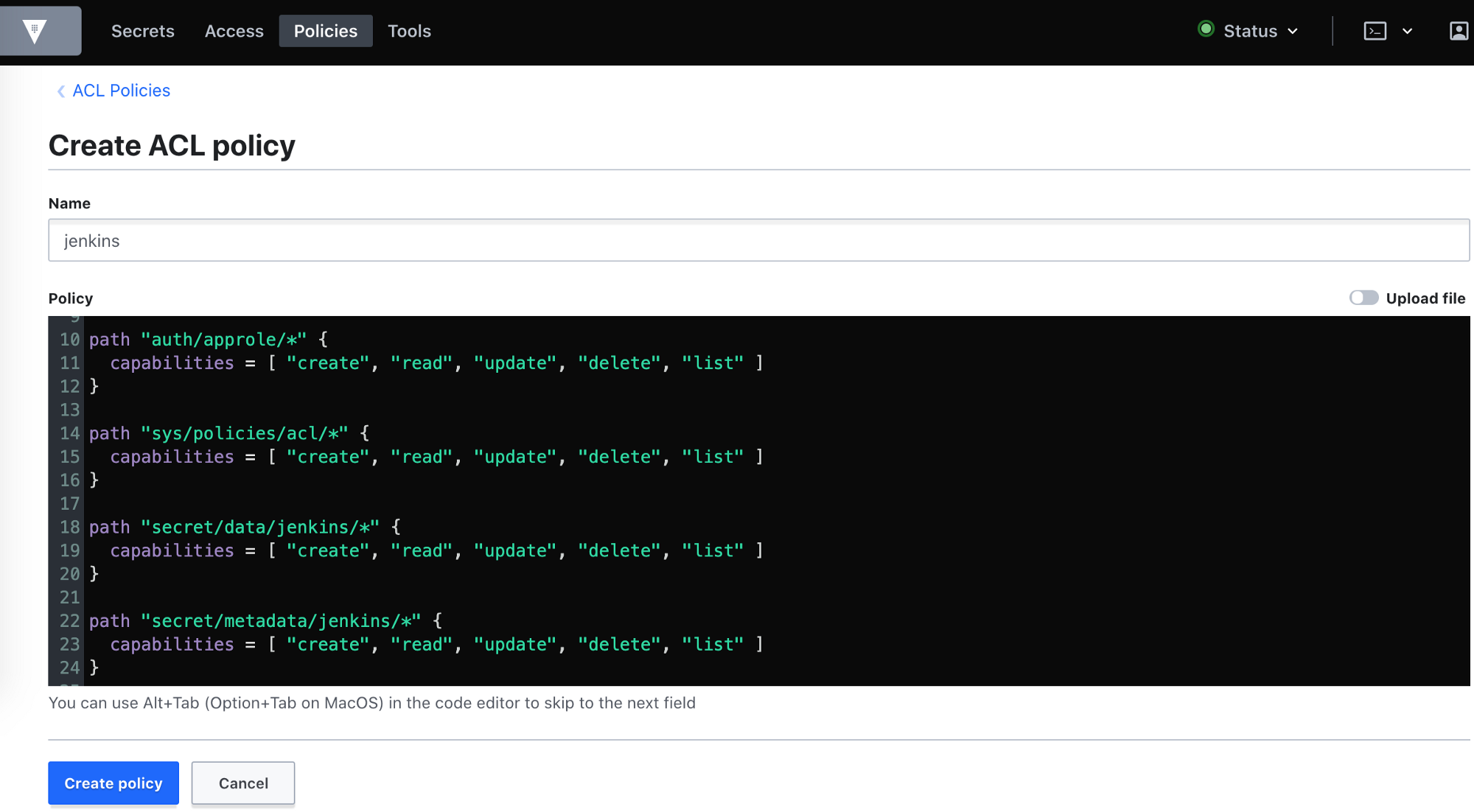
Another way for 3rd step (apply all needed policies) is to create a policy using Vault’s UI:
Go to policy tab -> Create ACL Policy
and then run via vault CLI:
Test that you created correctly role_id/secret_id
Testing authentication with vault using python hvac and appRole
Simple python script to test auth with vault:
first run ‘pip install hvac’.
I am running this script from pod with python container inside of my Kubernetes cluster.
URL of vault in k8s cluster: ‘http://vault.vault.svc.cluster.local:8200'
You will see authentication error if authentication is failed, if you do, make sure you applied all the needed policies, enabled applrole, and generated properly role_id / secret_id.
Validate role_id/secret_id is correct using vault CLI:
$ vault write auth/approle/login \
role_id=YOU_ROLE_ID \
secret_id=YOU_SECRET_ID
Get the list of secrets under ‘jenkins’ vault_prefix (CLI)
In my case, vault_prefix looks like: ‘secret/data/jenkins’ and all secrets stored under ‘jenkins’ prefix:
Each key in list has additional subset of keys, for example ‘aws’ has access_key_id/secret_access_keys
Getting the secrets list (python)
If you have a permissions error on the secrets list, check you have access to metadata, that what you should see in UI for ‘jenkins policy’:
If you don’t, add using the UI or vault CLI:
Get a specific secret (python)
If you have a permission error, check you have access to data in UI of Vault:
VaultHandler
I created VaultHandler which you can find here.
You can use it to:
- Dump all your secrets.
- Get a list of your secrets.
- Print all secrets nicely.
- Print all secrets drom dump.
- Populate Vault from dump to a specific ‘vault_prefix’.
Also, I think to extend it to use different auth methods, besides appRole, create CLI, to run it in the command line and much more :-)
If the idea sounds interesting, add stars to the repo or clone it, I will know this way you like the idea.
Create Jenkins scheduled job for daily vault backup
- I am using Vault Plugin in Jenkins https://plugins.jenkins.io/hashicorp-vault-plugin/ to add secrets as env variables during job execution. Read more about how to integrate this plugin into jenkins here: https://igorzhivilo.com/jenkins/how-to-read-vault-secrets-from-declarative-pipeline/
- During job execution POD will be created with 2 containers: awscli to use aws s3 utility, and push created encrypted dump to private s3 bucket (vault-backups), python to run VaultHandler.
Now create a new pipeline in jenkins: newitem -> pipeline and make it periodic (daily).
Conclusion
In this post, I described how to automate Vault backup creation using Jenkins scheduled job and simple python script which I built to create dump of vault secrets.
Thank you for reading, I hope you enjoyed it, see you in the next post.
If you want to be notified when the next post of this tutorial is published, please follow me here on medium and on Twitter (@warolv).
Original story on my blog: https://igorzhivilo.com/vault/scheduled-backup-vault-secrets/
Start blogging about your favorite technologies, reach more readers and earn rewards!
Join other developers and claim your FAUN account now!

Igor Zhivilo
DevOps Lead, warolv
@warolvUser Popularity
124
Influence
12k
Total Hits
2
Posts



















Only registered users can post comments. Please, login or signup.