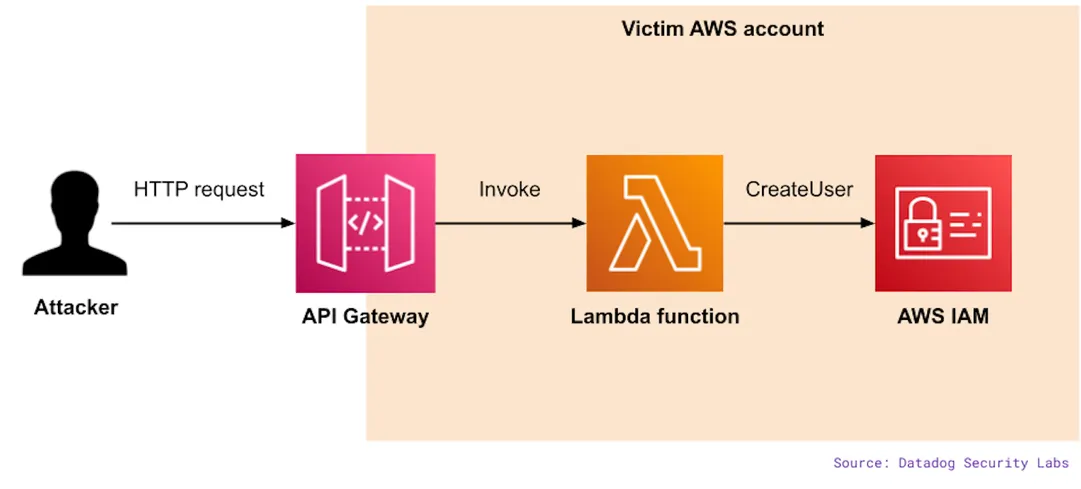
Hackers snagged some leaked AWS keys and conjured up a "persistence-as-a-service" scheme. They weaved through API Gateways and Lambda like ghostly threads. Dodging revocation? Easy. They whipped up dynamic IAM users faster than you can say "security breach." Telegram buzzed with ConsoleLogin events—automation winked in the shadows. They fiddled with SSO and MFA settings, stretching session durations to sidestep pesky security controls. A digital tightrope walk, if there ever was one.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















