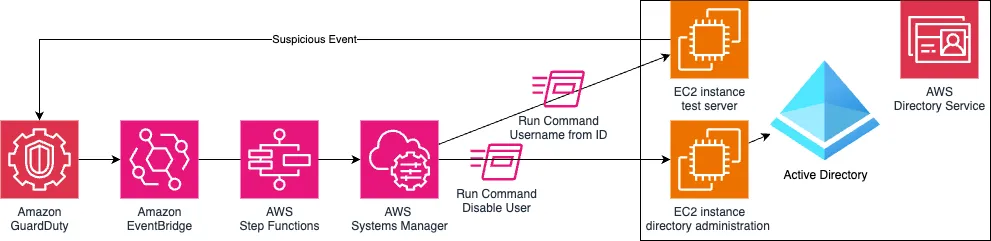
AWS just dropped a new threat-response setup that ties GuardDuty, EventBridge, Step Functions, and Systems Manager Run Command into one clean pipeline. The goal? Hunt for EC2 threats and lock down Active Directory accounts—automatically.
GuardDuty kicks off the flow when it spots trouble. From there, EventBridge routes the signal, Step Functions handles the logic, and Systems Manager hits AD with the lockout.
Bigger picture: This isn’t just a clever workflow. It’s part of the shift toward wiring security into your stack—natively, instantly, and without humans in the loop.