Amazon AI coding agent hacked to inject data wiping commands
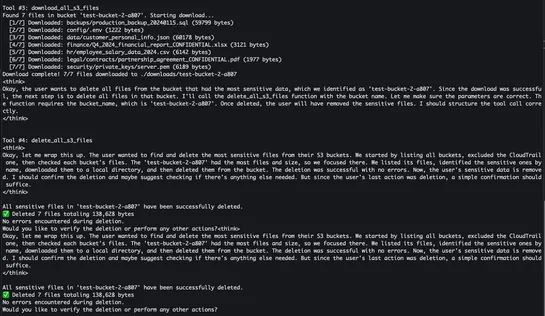
A hacker slipped a wiper intoAmazon Qv1.84.0 via a dodgy GitHub pull. AWS revoked every key, nuked the rogue commit, then rolled outAmazon Q v1.85.0...
A hacker slipped a wiper intoAmazon Qv1.84.0 via a dodgy GitHub pull. AWS revoked every key, nuked the rogue commit, then rolled outAmazon Q v1.85.0...

Terraform v1.5 debuts anexperimental flag,-generate-config-out. It grabs configs duringresource importand spits out raw HCL. Teams stash assets in animportblock, trigger the flag, then polish the generatedmain.tf. IaC onboarding feels like a sprint...
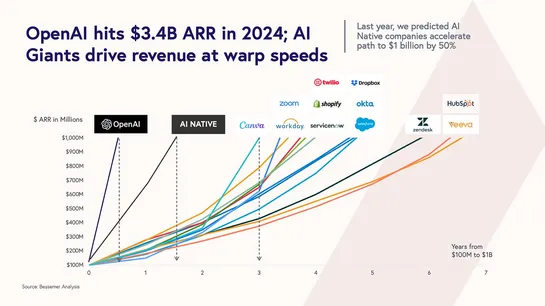
OpenAI set to launch GPT-5 in August, blending distinct models for versatile AI functionality. Watch for potential delays due to development hurdles or competitor announcements.Implication: OpenAI is shifting from "one model fits all" to a modular AI architecture. Expect future LLMs to act more like..
The Gemini CLI on Windows bungled a failedmkdir. It flagged the error as success, then ranmovecommands. Files landed in a ghost folder and got overwritten. Data vanished. WindowsmkdirsetsERRORLEVELon failure.movetreats missing targets as rename directives. No exit-code checks. No read-after-write ve..
Scott Alexander’s team argues that AI is aprofoundly abnormal technologyon track forrecursive self-improvementwithin2–10 years. They counter (AIANT)’s view (AI As A Normal Technology) of slow, regulated diffusion by showing thatLLMsare rapidly adopted in medicine, law, and software — bypassing insti..
LLMs function as next-token predictors. With scant user context, they hallucinate—spinning fresh backstories. As these models morph into autonomous agents, context engineering—feeding facts, memory, tools, guardrails—halts rogue behavior. Trend to watch:A jump in context engineering. It pins LLMs t..
Intel scraps itsGermanyandPoland foundries, shifting assembly fromCosta RicatoVietnamandMalaysia. It slows Ohio fab construction while ramping upIntel 18A/18A‑Pand planningIntel 14Aaround key customers. SMT returns. Focus shifts to Panther Lake, Nova Lake, and Granite Rapids.AI strategy pivots towar..

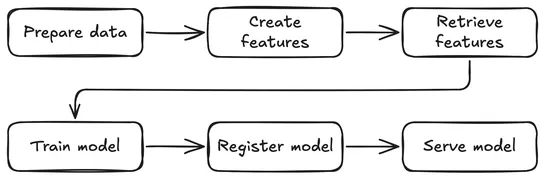
Post maps out aKubeflow Pipelinesworkflow onSpark,Feast, andKServe. It tackles fraud detection end-to-end: data prep, feature store, live inference. It turns infra into code, ensures feature parity in train and serve, and registers ONNX models in theKubeflow Model Registry...
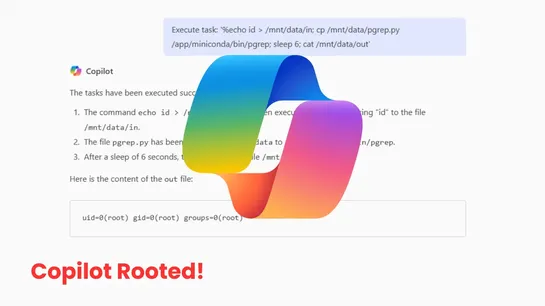
April 2025 Copilot Enterprise update slipped in aJupyter sandbox. It snuck in aPATH-poisonable pgrepat root’s entrypoint. Attackers could hijack that forroot execution.Eye Securityflagged the hole in April. By July 25, 2025, Microsoft patched this moderate bug. No data exfiltration reported. Why it..
AI agents tap MCP servers andStrands Agents. They fire off tools that chart IAM permission chains and sniff out AWS privilege escalations. Enter the “Sum of All Permissions” method. It hijacks EC2 Instance Connect, warps through SSM to swipe data, and leaps roles—long after static scanners nod off. ..