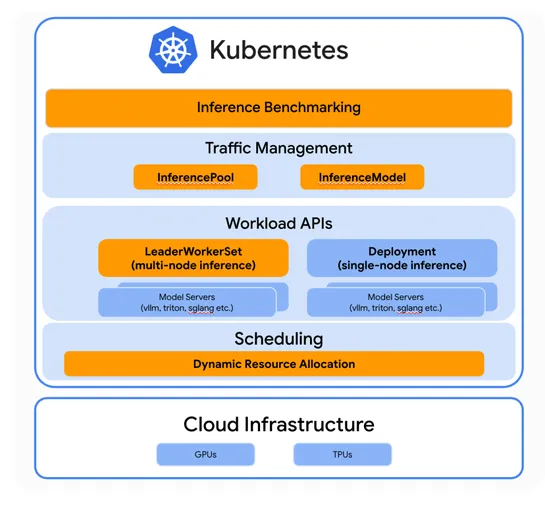
Evolving Kubernetes for generative AI inference
Google Cloud, ByteDance, and Red Hat are wiring AI smarts straight intoKubernetes. Think: faster inference benchmarks, smarter LLM-aware routing, and on-the-fly resource juggling—all built to handle GenAI heat. Their new push,llm-d, bakesvLLMdeep into Kubernetes. That unlocks disaggregated serving .. read more