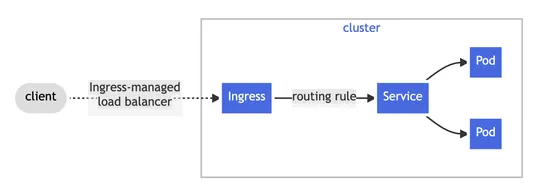
Why Kubernetes is retiring Ingress NGINX
The Kubernetes Steering Committee is pulling the plug onIngress NGINX- official support ends March 2026. No more updates. No security patches. Gone. Why? It's been coasting on fumes. One or two part-time maintainers couldn't keep up. The tech debt piled up. Now it's a security liability. What's next.. read more