🔐 𝗠𝗼𝘀𝘁 𝗰𝗼𝗺𝗽𝗮𝗻𝗶𝗲𝘀 𝘁𝗵𝗶𝗻𝗸 𝗻𝗲𝘁𝘄𝗼𝗿𝗸 𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗶𝘀 𝗮𝗯𝗼𝘂𝘁 𝘁𝗼𝗼𝗹𝘀.
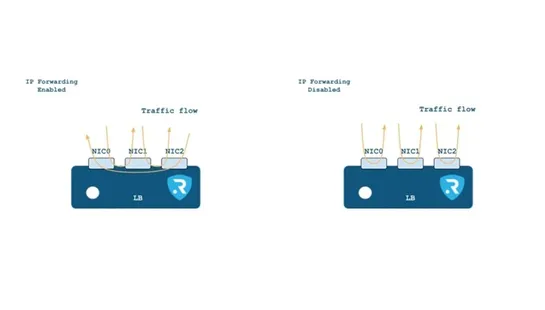
🔐 𝗠𝗼𝘀𝘁 𝗰𝗼𝗺𝗽𝗮𝗻𝗶𝗲𝘀 𝘁𝗵𝗶𝗻𝗸 𝗻𝗲𝘁𝘄𝗼𝗿𝗸 𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗶𝘀 𝗮𝗯𝗼𝘂𝘁 𝘁𝗼𝗼𝗹𝘀. Firewalls. WAFs. IDS. Monitoring platforms. But the truth is simpler: 𝗦𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝘀𝘁𝗮𝗿𝘁𝘀 𝘄𝗶𝘁𝗵 𝗮𝗿𝗰𝗵𝗶𝘁𝗲𝗰𝘁𝘂𝗿𝗲. At RELIANOID, we design our 𝗥𝗘𝗟𝗜𝗔𝗡𝗢𝗜𝗗 𝗟𝗼𝗮𝗱 𝗕𝗮𝗹𝗮𝗻𝗰𝗲𝗿 following the principles of 𝗜𝗦𝗢/𝗜𝗘𝗖 𝟮𝟳𝟬𝟯𝟯, the international framework for secure netwo..