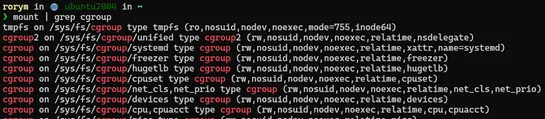
Container security fundamentals: Cgroups
A look at how cgroups are used in Linux and container systems.. read more
Join us
A look at how cgroups are used in Linux and container systems.. read more
Hey, sign up or sign in to add a reaction to my post.
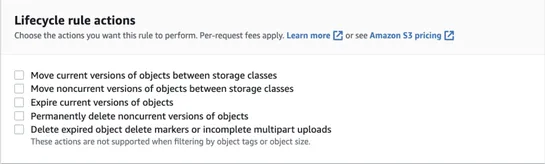
Find out how object lock can help prevent an object version from being modified or deleted to help combat ransomware attacks... read more
Hey, sign up or sign in to add a reaction to my post.
Learn how to use static application security testing (SAST) in your CI/CD pipelines to identify security vulnerabilities early in development and reduce risk... read more
Hey, sign up or sign in to add a reaction to my post.
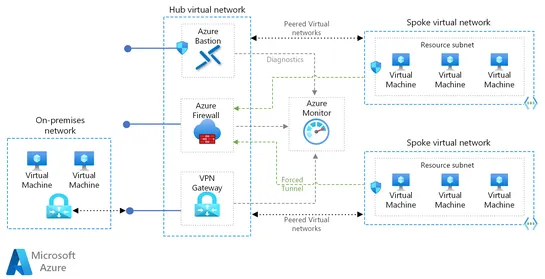
Few articles exist on alerting strategies, but this article aims to fill that gap by sharing valuable knowledge on developing a robust alerting system... read more
Hey, sign up or sign in to add a reaction to my post.
Azure DevOps CI/CD Pipeline with Terraform: a quick tutorial... read more
Hey, sign up or sign in to add a reaction to my post.
Azure Data Explorer now supports the ingestion of data from .NET Applications via theNLog sink... read more
Hey, sign up or sign in to add a reaction to my post.
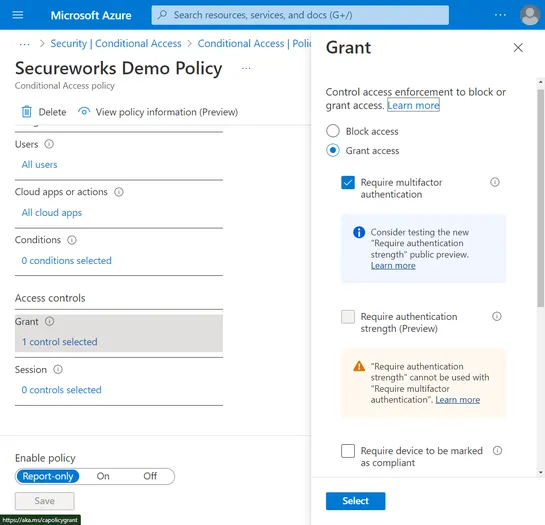
Learn how Secureworks Counter Threat Unit (CTU) researchers investigated which three APIs allow editing of CAP settings (Conditional Access policies)... read more
Hey, sign up or sign in to add a reaction to my post.
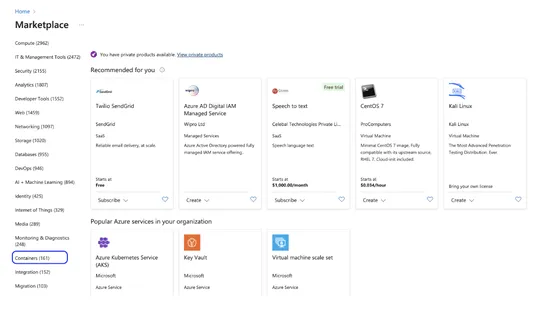
You'll learn how to deploy Isovalent Enterprise for Cilium on your AKS cluster from Azure Marketplace on a new cluster and also upgrade an existing cluster from an AKS cluster running Azure CNI powered by Cilium to Isovalent Enterprise for Cilium... read more
Hey, sign up or sign in to add a reaction to my post.
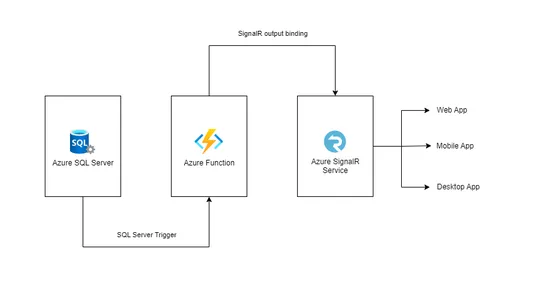
Using Azure Function with SQL trigger for change identification and Azure SignalR binding for notifications... read more
Hey, sign up or sign in to add a reaction to my post.
Microsoft Azure Cloud now has the capability to host "Confidential VMs", providing a new security offering to customers who need to protect their sensitive data while using computation in the cloud. The VMs leverage a confidential hardware platform to protect execution state and memory, and secure a.. read more
Hey, sign up or sign in to add a reaction to my post.
This tool doesn't have a detailed description yet. If you are the administrator of this tool, please claim this page and edit it.
Hey there! 👋
I created FAUN.dev(), an effortless, straightforward way for busy developers to keep up with the technologies they love 🚀
