Execution Client Diversity
Call to action: Node operators should diversify their execution clients away from a majority Geth setup.. read more
Join us
Call to action: Node operators should diversify their execution clients away from a majority Geth setup.. read more

Hey, sign up or sign in to add a reaction to my post.
Monero has become a popular cryptocurrency for cybercriminals to mine due to its value and low risk. SentinelOne recently detected a Monero mining campaign affecting Docker Linux systems, using simple obfuscation methods to evade detection and download a cryptocurrency mining program. Detection and .. read more

Hey, sign up or sign in to add a reaction to my post.
NIST Cybersecurity Framework 2.0 (NIST SCF 2.0) will reflect the evolving cybersecurity landscape and is expected to be published in 2024... read more
Hey, sign up or sign in to add a reaction to my post.
The Argo Project focuses on supply chain security and has made significant improvements in its security posture. It has adopted the SLSA framework, which provides a checklist of standards and controls to enhance security in software artifacts. Attestations play a crucial role in verifying the authen.. read more

Hey, sign up or sign in to add a reaction to my post.
Automate actions to enhance AWS Security Hub findings... read more

Hey, sign up or sign in to add a reaction to my post.
You can now get comprehensive account fraud prevention by combining AWS WAF Account Creation Fraud Prevention and Account Takeover Prevention in your AWS WAF web access control list (web ACL). This post shows you how to set up AWS WAF with ACFP for your application sign-up pages... read more

Hey, sign up or sign in to add a reaction to my post.
Two sleuthing SREs uncovered an AWS security issue. Here's how they found it, why it matters, and what you need to do to resolve it... read more

Hey, sign up or sign in to add a reaction to my post.
A Progess Software study found that many companies still don't understand DevSecOps, but they know securing their systems is a must... read more
Hey, sign up or sign in to add a reaction to my post.
New tools, a pre-built Hyper-V image, a new audio stack, and more!.. read more

Hey, sign up or sign in to add a reaction to my post.
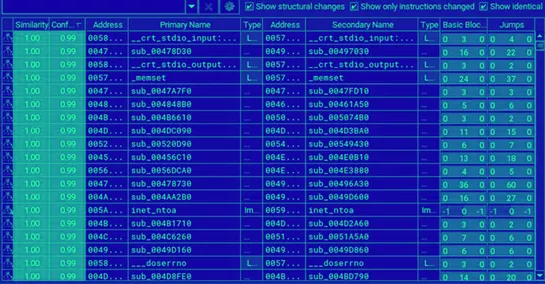
An analysis reveals striking similarities between the BlackSuit and Royal ransomware strains... read more
Hey, sign up or sign in to add a reaction to my post.
This tool doesn't have a detailed description yet. If you are the administrator of this tool, please claim this page and edit it.
Hey there! 👋
I created FAUN.dev(), an effortless, straightforward way for busy developers to keep up with the technologies they love 🚀
