Google accuses Microsoft of unfair practices in Azure cloud unit
Google filed a letter with the FTC, accusing Microsoft of overly restrictive licensing terms and said the company's influence poses cybersecurity risks... read more
Join us
Google filed a letter with the FTC, accusing Microsoft of overly restrictive licensing terms and said the company's influence poses cybersecurity risks... read more

Hey, sign up or sign in to add a reaction to my post.
Microsoft has announced new advances to Azure Quantum aimed at accelerating scientific discovery. This includes Azure Quantum Elements, which integrates high-performance computing, artificial intelligence, and quantum computing to reduce time and costs in R&D, increase the search space for new mater.. read more

Hey, sign up or sign in to add a reaction to my post.
An active campaign is targeting vulnerable SSH servers to covertly enlist them into a proxy network, allowing threat actors to leverage the victim's unused bandwidth for different services while reducing the chances of detection. The anonymity provided by proxyware services can also be exploited by .. read more
Hey, sign up or sign in to add a reaction to my post.
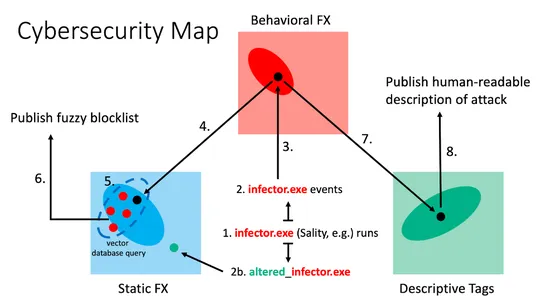
CrowdStrike data scientists have developed a new similarity paradigm that allows for the organization and accessibility of cybersecurity data. This paradigm enables scientists and analysts to effectively prevent and respond to breaches by associating different representations of important cybersecur.. read more
Hey, sign up or sign in to add a reaction to my post.
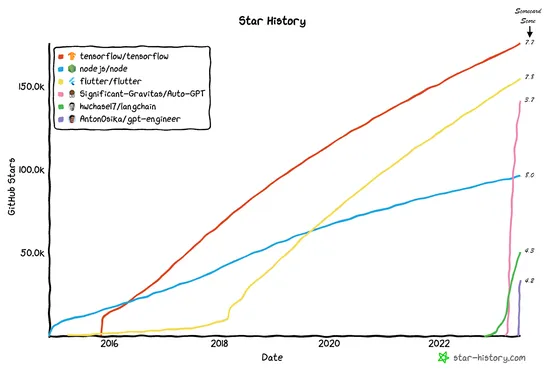
Generative AI, specifically Large Language Models (LLMs) like GPT, has revolutionized digital content creation. However, the security aspects of this technology are often overlooked, posing significant risks to organizations. The open-source ecosystem surrounding LLMs lacks maturity and security, ma.. read more
Hey, sign up or sign in to add a reaction to my post.
By combining Terraform, OPA, and Infracost, teams can automate infrastructure provisioning while ensuring best practices and cost constraints. The integration with GitHub Actions allows for early detection of potential issues and prevents unwanted changes from reaching the production environment... read more
Hey, sign up or sign in to add a reaction to my post.
Containers offer advantages such as efficient resource utilization and faster deployment. However, container security is crucial as they share the same kernel and vulnerabilities can pose risks to the host and other containers. Measures like namespace partitioning and control groups can help enhance.. read more

Hey, sign up or sign in to add a reaction to my post.
Researchers have found a flaw in Microsoft Azure AD which they claim can be used to take over accounts that rely on pre-established trust... read more

Hey, sign up or sign in to add a reaction to my post.
In 2022, there were 1802 recorded security breaches, impacting 422 million people—a 41% rise from the prior year. To prevent these breaches, organizations must prioritize strengthening their protection against cyber threats and understand different types of security breaches and real-world examples... read more
Hey, sign up or sign in to add a reaction to my post.
Patches have been issued by Grafana for a critical security flaw that could allow accounts to be hijacked when using Azure Active Directory for authentication. Organizations are advised to upgrade to the latest version of Grafana or take mitigating actions... read more
Hey, sign up or sign in to add a reaction to my post.
This tool doesn't have a detailed description yet. If you are the administrator of this tool, please claim this page and edit it.
Hey there! 👋
I created FAUN.dev(), an effortless, straightforward way for busy developers to keep up with the technologies they love 🚀
