How Kubernetes Became the New Linux
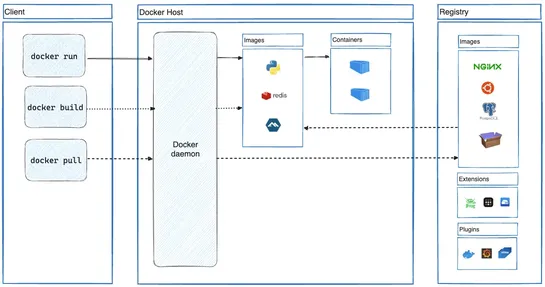
AWS just handed overKarpenterandKubernetes Resource Orchestrator (Kro)to Kubernetes SIGs. Big move. It's less about AWS-first, more about playing nice across the ecosystem. Kroauto-spins CRDs and microcontrollers for resource orchestration.Karpenterhandles just-in-time node provisioning - leaner, fa.. read more



![Kubernetes Tutorial For Beginners [72 Comprehensive Guides]](https://cdn.faun.dev/prod/media/public/images/kubernetes-tutorial-for-beginners.width-545.format-webp.webp)