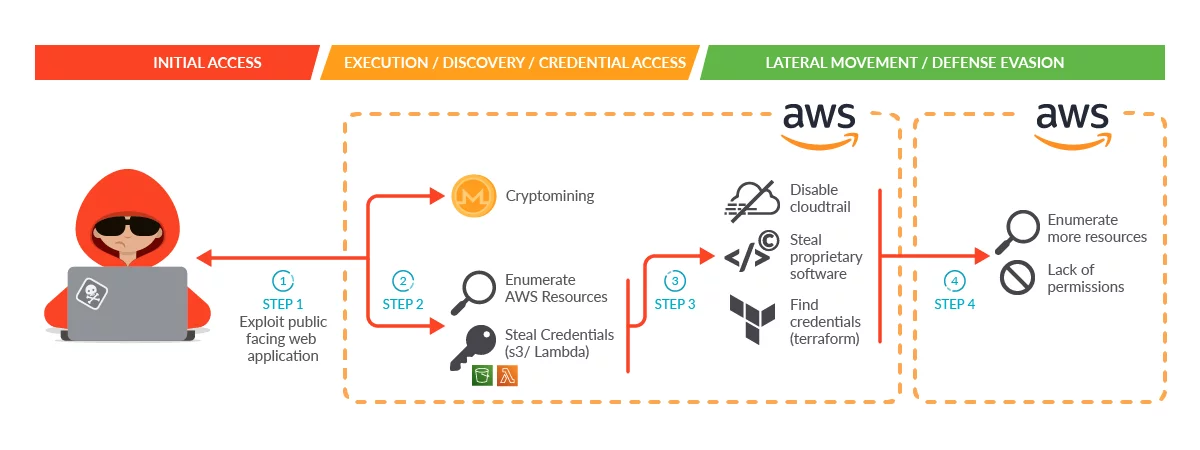
The SCARLETEEL attack was a sophisticated cloud operation that exploited a containerized workload to gain access to an AWS account and steal proprietary software and credentials. The attacker used knowledge of AWS cloud mechanics, such as EC2 roles, Lambda serverless functions, and Terraform, to perform privilege escalation and attempt to pivot to other connected AWS accounts.
To reduce the risk from advanced threats, organizations should use tools such as virtual machine, cloud security posture management (CSPM), cloud infrastructure entitlement management (CIEM), runtime threat detection, and secrets management. Additionally, patching and applying a vulnerability management cycle to public-facing containers and using IMDS v2 instead of IMDS v1 can help prevent unauthorized access. Adopting the principle of least privilege and scoping read-only access on specific AWS resources can also reduce the risk of compromise.
Finally, storing the Terraform state file in a secure location and using key management services (KMSs) to encrypt and decrypt secrets as needed can help keep sensitive information safe. The SCARLETEEL attack highlights the importance of zero trust, the principle of least privilege, strong detections and alerts, and ongoing security measures to reduce the likelihood of compromise in cloud environments.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















