The blog post introduces the MitreMap Notebook, a tool that allows SecOps teams to input a threat report and infer the most likely MITRE ATT&CK technique(s) that map to the report.
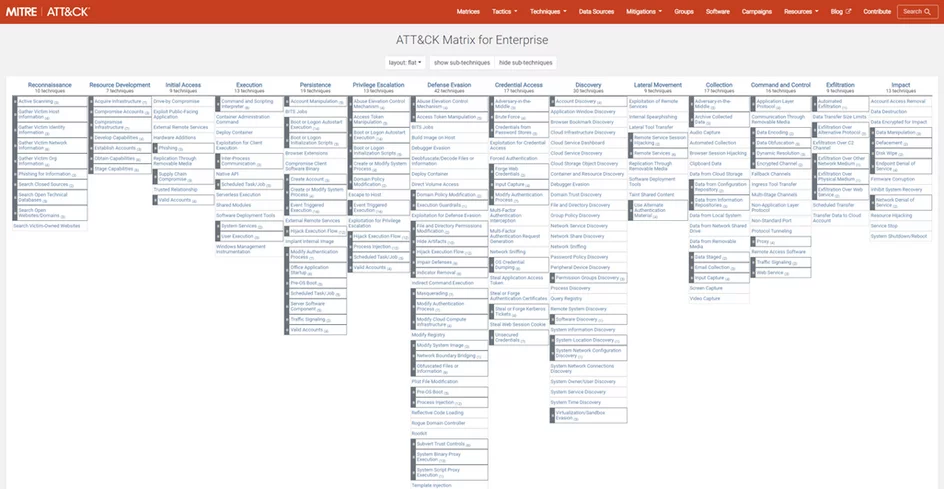
The MITRE ATT&CK framework is used to standardize the discovery and explanation of attacker behavior, providing a knowledge base of TTPs used by adversaries across enterprise, mobile, and ICS applications.
The MitreMap Notebook uses Natural Language Processing to extract actionable intelligence from unstructured threat intelligence data, identifying the associated motivations and TTPs used by an actor group when carrying out an attack on an enterprise’s digital infrastructure.
The notebook is currently in public preview in the Microsoft Sentinel Notebooks repository, and the documentation for setting up, configuring, and running the notebook can be found in the blog post.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















