In this post, the author explores the fundamental concept that containers are processes, just like any other application running directly on the host operating system. This means that existing Linux tools can be used to interact with and debug containerized environments.
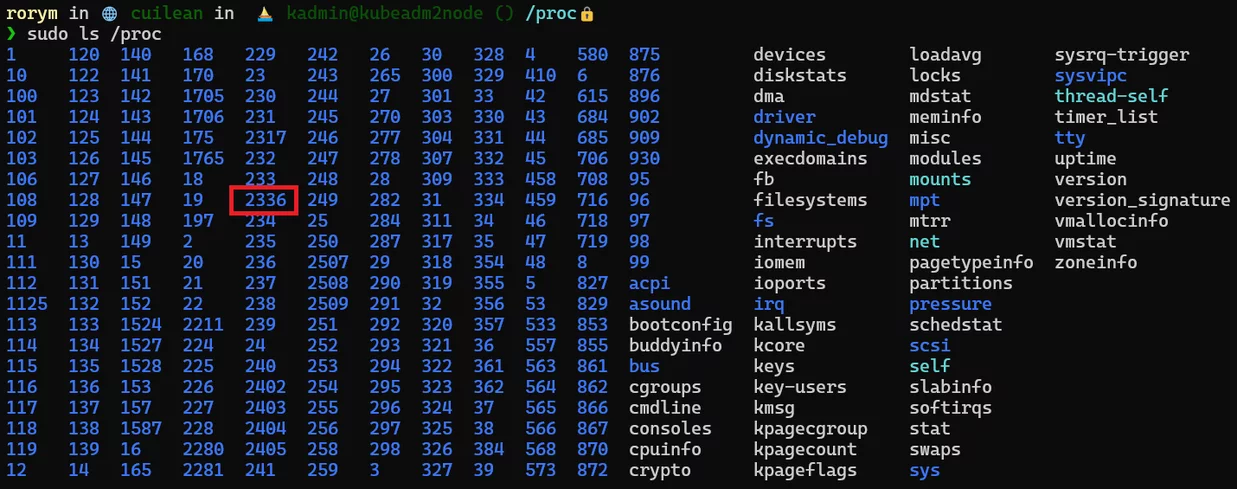
The /proc filesystem can be used to access information about running containers, and it can also be used to navigate to a container's root filesystem and edit files. However, it's important to note that anyone with access to the underlying host can use process lists to see information about running containers, including sensitive information like environment variables. This has implications for container security, which will be explored further in upcoming parts of this series.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















