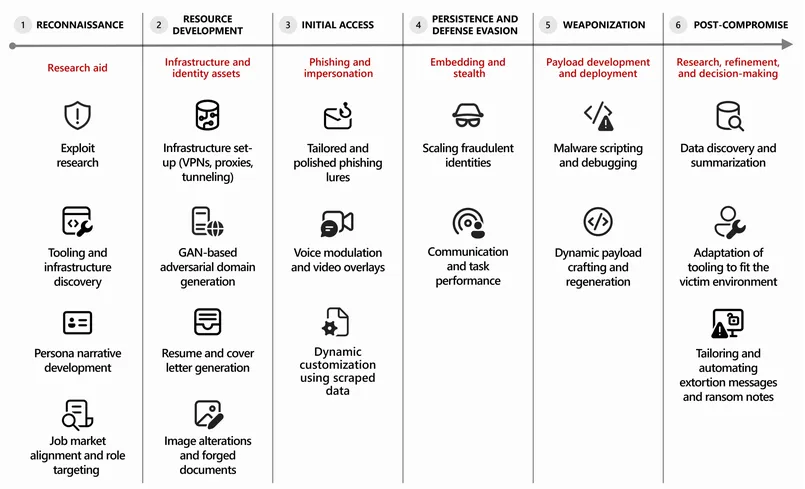
Microsoft observes threat actors operationalize AI and LLMs across the cyberattack lifecycle. They accelerate reconnaissance, phishing, malware development, and post‑compromise triage.
Actors abuse jailbreaking techniques and GANs. They craft personas, generate look‑alike domains, embed runtime‑adaptive payloads, and bypass EDR and model safeties.
Microsoft introduced the Security Dashboard for AI, Prompt Shields, Groundedness Detection, Microsoft Defender XDR, and Microsoft Security Copilot. Controls like DSPM, ZAP, MFA, and Purview help detect and govern AI‑enabled threats.