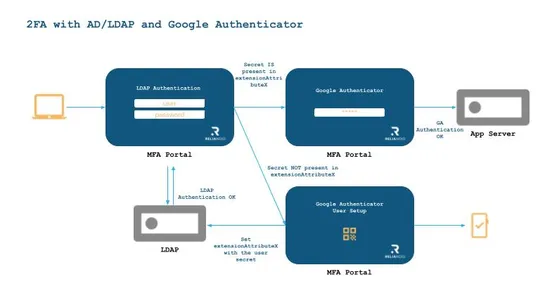
Strengthen Your MFA with Google Authenticator and RELIANOID
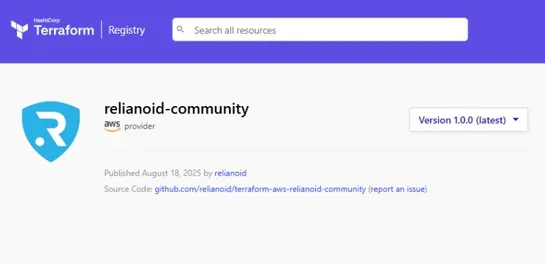
🔐 Strengthen Your MFA with Google Authenticator and RELIANOID At RELIANOID, we take authentication seriously. We've just published a new technical guide on how to integrate Google Authenticator into the RELIANOID MFA Portal, using Active Directory or LDAP to manage user secrets. ✅ Understand TOTP vs..