Aggressive bots ruined my weekend
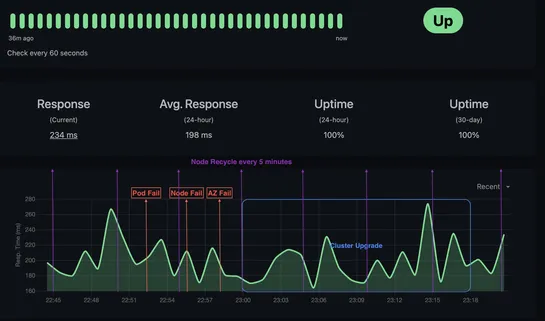
Bear Blog went dark after getting swarmed by scrapers. The reverse proxy choked first - too many requests, not enough heads-up. Downstream defenses didn’t catch it in time. So: fire, meet upgrades. What changed: Proxies scaled 5×. Upstream got strict with rate limits. Failover now has a pulse. Resta.. read more