The Green Tea Garbage Collector
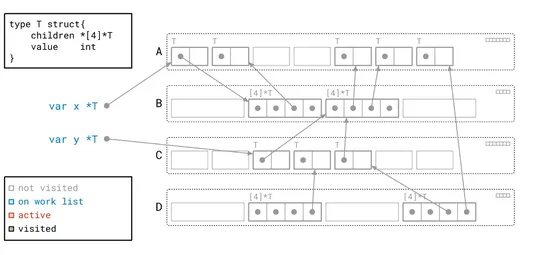
Go 1.25 drops an experimental GC calledGreen Tea. It flips the script on object traversal - scanning memory pages instead of hopping from object to object. The payoff? Up to40% less GC CPU overheadon real workloads. Bonus: it taps intoAVX-512on newer x86 chips forvectorized scanning. Turns out strea.. read more