You Want Microservices—But Do You Need Them?
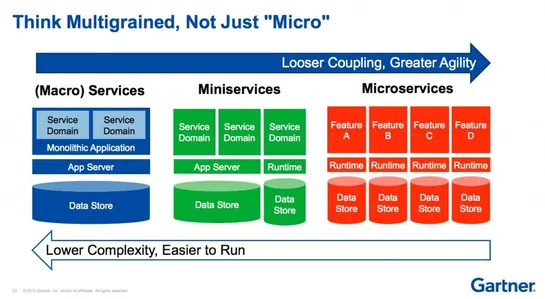
Amazon Prime Video ditched its pricey microservices maze and rebuilt as asingle-process monolith, cutting ops costs by 90%. No big press release. Just results. Same move from Twilio Segment. And Shopify. Both pulled their tangled systems back intomodular monoliths- cleaner, faster, easier to test, a.. read more