🚗🔐 Automotive Cybersecurity: Connected Cars and a Vulnerable Supply Chain
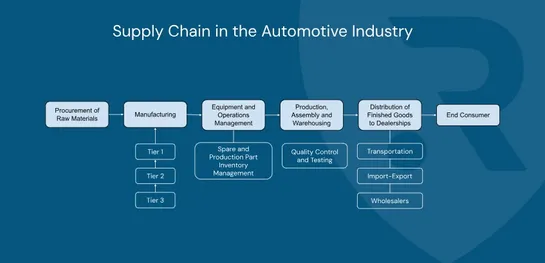
We originally published this article back in November, but it remains highly relevant today. Sharing it again in case you missed it 👇 Connected cars are no longer just mechanical machines — they are computers on wheels, embedded in complex digital ecosystems. As shown in the “Supply Chain in the aut..