Securing Agents in Production (Agentic Runtime, #1)
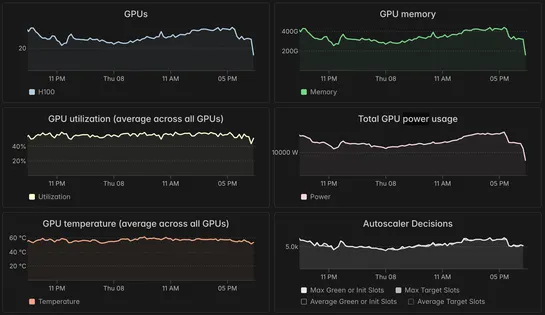
Palantir's AIP Agentic Runtime isn't just another agent platform, it's a control plane with teeth. Think tight policy enforcement, ephemeral autoscaling with Kubernetes (Rubix), and memory stitched in from the jump viaOntology. Tool usage? Traced and locked down with provenance-based security. Every.. read more