Reversing YouTube's "Most Replayed" Graph
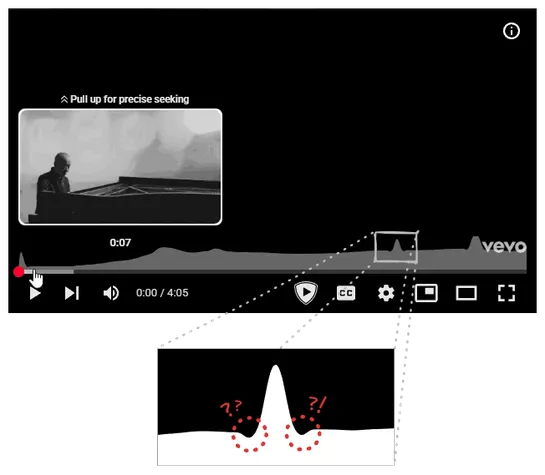
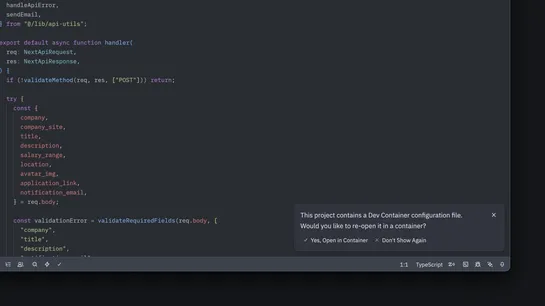
An engineer cracked open YouTube’s “most replayed” heatmap. Turns out it runs onsampled view frequency arrays, client-sidenormalization, andSVG renderingstitched together withCubic Bézier splinesfor that smooth, snappy curve. Behind the scenes, playback gets logged with adifference array + prefix su.. read more