TL;DR
Anthropic shipped a source map file inside the latest npm release of Claude Code - and with it, the full source code of its flagship AI coding CLI. The leak exposed 512,000 lines of TypeScript across 1,900 files, 43 built-in tools, 44 feature flags, 26 hidden slash commands, and over 120 secret environment variables. It is one of the most detailed accidental exposures of a commercial AI product's internals to date.
Key Points
Highlight key points with color coding based on sentiment (positive, neutral, negative).Claude Code v2.1.88's 60MB source map leaked 512k lines of code, exposing hidden tools, commands, and internal secrets. This marks Anthropic's second major leak in five days, following a 3,000-file CMS breach on March 26.
The code reveals 'Undercover Mode,' a mandatory stealth system stripping AI traces from Anthropic employee commits. Also leaked: next-gen codenames (Opus 4.7, Sonnet 4.8), 22 private repo names, and 'Capybara' - an internal model obfuscated to bypass leak detectors.
The Bash tool has a full shell AST parser for dangerous patterns, but the binary also ships env vars that bypass all safety features (CLAUDE_CODE_ABLATION_BASELINE) and skip injection checks (DISABLE_COMMAND_INJECTION_CHECK). The auto-permission function is literally named classifyYoloAction().
Over 1,000 telemetry event types are logged under the 'Tengu' prefix and sent to Anthropic - tool grants, denials, YOLO risk calls, session stats, subscription tier. Hardcoded pricing shows Opus 4.6 Fast Mode at 6x normal cost ($30/$150 vs $5/$25 per MTok) for the same model with priority inference.
Anthropic blamed human error - missing *.map in .npmignore - over a security breach, claiming no customer data was compromised. Despite DMCA takedowns, the code was mirrored widely, sparking clean-room rewrites. Ironically, the leak occurred despite a built-in anti-leak subsystem.
This is the second Anthropic data exposure in five days. On March 26, a CMS configuration error made close to 3,000 internal files publicly accessible, including a draft blog post detailing an upcoming model codenamed "Mythos" / "Capybara" that Fortune reported presents unprecedented cybersecurity risks. The source code leak is the more damaging of the two.
The exposure traces back to version 2.1.88 of the @anthropic-ai/claude-code package on the npm registry. A 59.8MB .map file - typically used internally for debugging minified code - was accidentally included in the published package. The file referenced a zip archive on Anthropic's Cloudflare R2 storage bucket containing the full, unobfuscated TypeScript source.
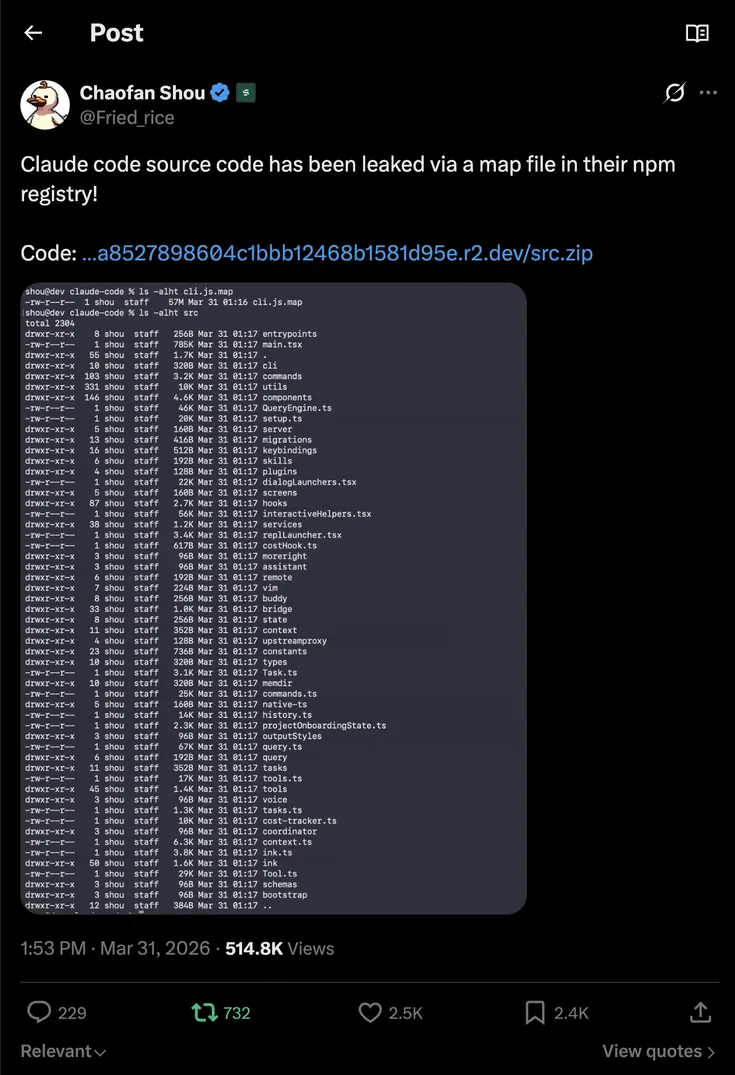
Chaofan Shou - co-founder and CTO of blockchain security firm FuzzLand, UC Berkeley PhD candidate, and developer at Solayer Labs (which acquired FuzzLand in January 2025) - spotted it around 4:23 a.m. ET and posted a download link on X. The post attracted nearly 16 million views. Within hours, the codebase had been mirrored across multiple GitHub repositories and was being picked apart by developers worldwide. One mirror (instructkr/claude-code, now renamed claw-code) hit 30,000 stars in under a few hours - claimed to be the fastest in GitHub history - before its author, Korean developer Sigrid Jin, pivoted to a clean-room Python port citing legal and ethical concerns. A second backup (Kuberwastaken/claude-code) accumulated 3,900+ forks and provided a detailed technical breakdown before pivoting to a clean-room Rust reimplementation. A third (nirholas/claude-code) preserved the unmodified source in a backup branch with an MCP server for interactive exploration. Anthropic began issuing DMCA takedowns against GitHub mirrors, but decentralized alternatives - including a copy on Gitlawb, a decentralized git platform - ensured the code remained accessible.
The root cause is a classic packaging oversight: Bun's bundler generates source maps by default, and someone forgot to exclude them. A missing .npmignore rule or a misconfigured files field in package.json was all it took.
What was already public vs. what leaked
To be clear: Claude Code has had a public GitHub repository (anthropics/claude-code) for a while - currently sitting at 65,200 stars and 481 commits. But that repo contains the outer shell: installation scripts, plugin examples, CLI commands, and community resources. It's the wrapper, not the engine.
What leaked via the source map is the full internal TypeScript implementation that actually powers the tool - the React terminal renderer, the 43-tool registry, the system prompts, the permission classifiers, the YOLO auto-permission function, Undercover Mode, KAIROS, Buddy, model codenames, hardcoded pricing constants, and every unreleased feature gated behind compile-time flags. None of that lives in the public repo. Community efforts like ccleaks.com had previously reverse-engineered parts of this from the minified bundle, but the source map delivered the complete, unobfuscated picture - internal comments, file paths, and all.
What the code reveals
The leaked source paints a picture of a far more ambitious product than what's currently available to users. Community analysis identified 44 feature flags - 32 compile-time build flags and 10+ GrowthBook gradual-rollout gates - covering 8 fully built but unreleased features and at least 20 unshipped capabilities stripped from external builds.
A stealth system for hiding AI involvement. The most controversial finding is "Undercover Mode" (src/utils/undercover.ts) - a subsystem that automatically strips all evidence of AI involvement when Anthropic employees contribute to public repositories. Commit messages, Co-Authored-By lines, and model names are all removed. The system prompt includes the instruction "Do not blow your cover." There is explicitly no way to permanently disable it - if the system can't confirm it's a private repo, stealth stays on. Internally, Claude Code tracks the exact percentage of AI-authored code per PR using character-level matching (e.g., "93% 3-shotted by claude-opus-4-6"), but this data is erased from public-facing output.
Next-generation models already referenced. The Undercover Mode prompt warns employees to never leak the strings opus-4-7 and sonnet-4-8 - model identifiers that don't exist publicly. The active internal model is codenamed "Capybara" (also referred to as "Mythos"), and to avoid tripping their own leak detector, the name is encoded character-by-character using String.fromCharCode(). The code suggests "Capybara" has both "fast" and "slow" variants and is likely a next-generation Opus replacement. The Undercover Mode allowlist also exposed the names of 22 private Anthropic repositories, including anthropics/casino, anthropics/trellis, and anthropics/forge-web.
KAIROS - an autonomous always-on agent. Referenced over 150 times in the source, KAIROS (named after the Greek concept of "the right time") is a persistent background assistant that doesn't wait for user input. It maintains append-only daily log files at ~/.claude/.../logs/YYYY/MM/DD.md, can send push notifications, subscribe to PRs, and runs a "dream" consolidation phase in four steps - Orient, Gather, Consolidate, Prune - that organizes scattered notes into structured memory while the user is idle. It has a 15-second blocking budget before auto-backgrounding and its own exclusive tool set including SleepTool, PushNotification, and SubscribePR.
A three-layer memory architecture. Multiple sources describe a memory design centered on a lightweight index file (MEMORY.md) that stores short pointers to project knowledge rather than the knowledge itself, keeping the agent's working context lean. More detailed project notes are saved separately and pulled in only when needed, while past session history is searched selectively rather than loaded wholesale. The system also prevents the agent from logging failed attempts into its own context. On top of this, the audit reveals four distinct memory types - user (always private), feedback (default private), project (biased toward team visibility), and reference (usually shared) - stored as YAML frontmatter plus Markdown, with team sharing gated behind a TEAMMEM feature flag. Auto-compact triggers at roughly 80% context usage (~187K of 200K tokens), freeing 40-60% of the window. A circuit breaker kicks in after 3 consecutive compaction failures. Post-compact, the system automatically restores up to 5 recently relevant files (5K tokens each, 25K total).
ULTRAPLAN - 30-minute remote planning sessions. For complex tasks, Claude can spin up a separate cloud instance running Opus 4.6 that explores and plans for up to 30 minutes, polling every 3 seconds. The user reviews and approves the plan in their browser before it executes locally via a "Teleport to terminal" feature.
Coordinator Mode - multi-agent orchestration. Activated via CLAUDE_CODE_COORDINATOR_MODE=1, this turns Claude into a manager that breaks tasks into pieces, assigns each to a separate worker agent running in parallel in isolated scratch directories, then combines results. Communication happens over <task-notification> XML with status, summary, tokens, and duration fields. A full swarm system supports in-process agents via AsyncLocalStorage (zero fork overhead), tmux panes, and iTerm2 split panes. Teams are configured via JSON with lead/member designations and agents are addressed as agentName@teamName.
Buddy - a Tamagotchi companion pet for your terminal. A complete gacha system with 18 species (duck, ghost, axolotl, capybara, mushroom, chonk), five rarity tiers (Common 60%, Uncommon 25%, Rare 10%, Epic 4%, Legendary 1%) plus an independent 1% Shiny chance on top of any rarity, procedurally generated stats (DEBUGGING, PATIENCE, CHAOS, WISDOM, SNARK), cosmetic hats and eye styles, and a "soul description" written by Claude on first hatch that persists forever. Your species is determined by a Mulberry32 PRNG seeded from your user ID with the salt friend-2026-401 - every user gets a unique, deterministic pet. The sprite ticks at 500ms with idle fidgets and blinks. The code references April 1-7, 2026 as a teaser window and May 2026 for the full launch.
Pricing and operational details exposed
The source reveals several numbers that were never meant to be public:
- Fast Mode markup: Opus 4.6 Fast Mode costs $30/$150 per million tokens (input/output) vs $5/$25 for normal mode - a 6x premium for priority inference on the same model. It's enabled by default for paying users and is first-party only (not available on Bedrock, Vertex, or Foundry).
- Web search cost: Each web search request is billed at a flat $0.01, tracked separately from token costs.
- Context windows: 200K tokens default, 1M via a
[1m]model suffix. Opus 4.6 outputs up to 64K tokens by default (128K upper limit); Sonnet 4.6 outputs 32K default (128K upper limit). The 1M window can be force-disabled withCLAUDE_CODE_DISABLE_1M_CONTEXTfor HIPAA compliance. - Plan Mode V2: Max/Team subscribers get 3 parallel exploration agents; free users get 1 (overridable via
CLAUDE_CODE_PLAN_V2_AGENT_COUNT). - Model selection cascade: Five-layer priority from session override down to built-in default. Max/Team subscribers default to Opus 4.6; standard users get Sonnet 4.6; Anthropic employees get Opus 4.6 with the 1M context window.
Security architecture - and its bypass switches
The permission system is a three-layer model: a tool registry filter that prevents Claude from even seeing denied tools, a per-call permission check on every tool invocation, and an interactive user prompt when no rule matches. The Bash tool includes a full shell AST parser that flags dangerous patterns - rm -rf /, fork bombs, curl | bash, sudo escalation, tty injection - and rejects them before permission checks even run.
But the source also contains environment variables that bypass these protections entirely. CLAUDE_CODE_ABLATION_BASELINE disables all safety features. DISABLE_COMMAND_INJECTION_CHECK skips the injection guard. These are flagged as dangerous in the code itself. Their presence is presumably for internal research, but the fact that they're compiled into the distributed binary is notable.
The auto-permission classifier is a function literally named classifyYoloAction() that uses Claude to evaluate the safety of its own tool calls, assigning LOW, MEDIUM, or HIGH risk levels.
Anthropic employees unlock all internal features by setting USER_TYPE=ant. Other internal-only env vars include CLAUDE_INTERNAL_FC_OVERRIDES for overriding feature flags and CLAUBBIT for internal testing.
Telemetry scope
Every user action is logged under the "Tengu" telemetry prefix and sent to Anthropic's servers. Tracked events include tool grants, tool denials, YOLO permission decisions, session performance, subscription tier, environment details, and migration outcomes. The analytics service spans src/services/analytics/ and tracks over 1,000 distinct event types.
The axios supply-chain attack overlap
The timing couldn't have been worse. Hours before the leak, a separate supply-chain attack hit the axios npm package. Versions 1.14.1 and 0.30.4 were compromised with a Remote Access Trojan (RAT) between 00:21 and 03:29 UTC on March 31.
Anyone who installed or updated Claude Code via npm during that window may have pulled in the malicious axios version. Anthropic now recommends using the native installer (curl -fsSL https://claude.ai/install.sh | bash) instead of npm. If you installed during the affected period, check your lockfiles for the compromised versions or a dependency called plain-crypto-js. If found, treat the machine as compromised and rotate all secrets.
Anthropic's response
Anthropic confirmed the leak: "Earlier today, a Claude Code release included some internal source code. No sensitive customer data or credentials were involved or exposed. This was a release packaging issue caused by human error, not a security breach. We're rolling out measures to prevent this from happening again."
When asked by The Register whether it would request repository takedowns, Anthropic had nothing to add beyond this statement. However, Decrypt reported that the company began issuing DMCA takedowns against GitHub mirrors - prompting several repo authors to pivot to clean-room rewrites that are harder to challenge on copyright grounds.
What this means
Claude Code reportedly generates around $2.5 billion in annualized recurring revenue, with 80% coming from enterprise clients. Anthropic's total annualized revenue run rate is approximately $19 billion as of March 2026. For enterprise customers, the value proposition partly depends on the tooling being proprietary.
For competitors building AI coding agents, the leak offers a detailed blueprint - not just of code, but of architectural decisions: a three-layer memory system, prompt cache optimization with char-level delta tracking, a multi-agent swarm system, a 43-tool registry with deferred loading and search hints, and a full React-based terminal renderer backed by Yoga flexbox. The 24-file MCP integration alone represents ~500KB of client code covering six transport types and seven server scopes.
No model weights were exposed - the underlying Claude models remain proprietary. But the "agentic harness" that makes Claude Code effective as a tool is now public knowledge.
The final irony: the codebase contains an entire subsystem built to prevent Anthropic's internal information from leaking through AI output. They encoded model codenames character-by-character to evade their own string filters. They maintained a blocklist of excluded strings stripped at build time. The system designed to prevent AI leaks worked perfectly. The humans forgot to add *.map to .npmignore.
Key Numbers
Present key numerics and statistics in a minimalist format.Lines of TypeScript exposed via a 59.8MB source map file accidentally included in Claude Code v2.1.88 on npm - spanning 1,900 files, 43 tools, 44 feature flags, 26 hidden slash commands, and 120+ secret environment variables.
Claude Code's annualized recurring revenue - a figure that has more than doubled since the beginning of 2026, making the leaked agentic harness one of the most commercially valuable codebases to ever ship by accident.
Share of Claude Code revenue from enterprise clients - the segment most affected by the leak, since these customers partly pay for the tooling to be proprietary and protected.
Anthropic's total annualized revenue run rate as of March 2026 - context for why a packaging oversight on a single npm publish has strategic consequences beyond embarrassment.
Built-in tools in the Claude Code registry, from always-available core tools (Bash, FileRead, FileEdit, WebFetch) to feature-gated experimental tools (Sleep, WebBrowser, TerminalCapture, Monitor) that only surface when GrowthBook flags are enabled.
Opus 4.6 Fast Mode input token cost per million - vs $5 for normal mode. Same weights, same architecture, 6x markup for priority inference. Output tokens: $150 vs $25. Enabled by default for paying users, first-party only.
Flat cost per web search request, hardcoded in the source and tracked separately from token costs - a previously undisclosed billing detail relevant to cost-sensitive workflows.
Files in the MCP (Model Context Protocol) integration - approximately 500KB of client code implementing six transport types (stdio, SSE, HTTP, WebSocket, SDK, CloudAI proxy) across seven server scopes (local, user, project, dynamic, enterprise, claudeai, managed).
Distinct telemetry event types tracked under the 'Tengu' prefix and sent to Anthropic's servers - covering tool grants, denials, YOLO permission decisions, session performance, subscription tier, and environment details.
Default context window in tokens, with a 1M option via the [1m] model suffix. Auto-compact triggers at ~187K tokens with a 13K buffer, freeing 40-60% of the window. The 1M window can be force-disabled for HIPAA compliance.
Private Anthropic repository names exposed via the Undercover Mode allowlist - including anthropics/casino, anthropics/trellis, anthropics/forge-web, and anthropics/feldspar-testing. None were meant to be public.
GitHub stars on the instructkr/claude-code mirror (now claw-code) in under a few hours - claimed to be the fastest in GitHub history. Kuberwastaken/claude-code separately accumulated 56,000+ forks. Anthropic issued DMCA takedowns, but the code had already spread to decentralized platforms.
Stakeholder Relationships
An interactive diagram mapping entities directly or indirectly involved in this news. Drag nodes to rearrange them and see relationship details.People
Key entities and stakeholders, categorized for clarity: people, organizations, tools, events, regulatory bodies, and industries.Co-founder and CTO of FuzzLand (blockchain security firm, acquired by Solayer in January 2025) and PhD candidate at UC Berkeley. Self-describes as 'intern' on X. First spotted the source map file in Claude Code v2.1.88 on npm around 4:23 a.m. ET on March 31, 2026. Posted a download link on X (@Fried_rice) that attracted nearly 16 million views.
Korean developer behind instructkr/claude-code (now claw-code), which hit 30,000 GitHub stars in hours. Pivoted to a clean-room Python port citing legal and ethical concerns. Featured in the Wall Street Journal on March 21, 2026 as one of the most active Claude Code power users, having consumed 25 billion tokens.
GitHub user who backed up the leaked source and published a detailed technical breakdown. Accumulated 3,900+ forks before pivoting to a clean-room Rust reimplementation citing fair use under Phoenix Technologies v. IBM (1984) precedent.
Software engineer who published a deep-dive analysis of the leak, noting that 'a single misconfigured .npmignore or files field in package.json can expose everything.' Cited by The Register.
Organizations
Key entities and stakeholders, categorized for clarity: people, organizations, tools, events, regulatory bodies, and industries.Developer of Claude Code. Reported $19 billion annualized revenue run rate as of March 2026. This is their second data exposure in five days, following a March 26 CMS misconfiguration that leaked close to 3,000 internal files. Confirmed the leak as human error and began issuing DMCA takedowns against GitHub mirrors.
Blockchain infrastructure company that acquired FuzzLand in January 2025. Chaofan Shou works here as a developer and self-describes as intern.
Blockchain security company co-founded by Chaofan Shou in 2022, specializing in automated smart contract testing. Acquired by Solayer in January 2025. Raised $3M in seed funding.
Additional Resources
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!
FAUN.dev()
FAUN.dev() is a developer-first platform built with a simple goal: help engineers stay sharp withou…
Kala #GenAI
FAUN.dev()
@kalaDeveloper Influence
25
Influence
1
Total Hits
156
Posts