The best tools for bare metal automation that people actually use
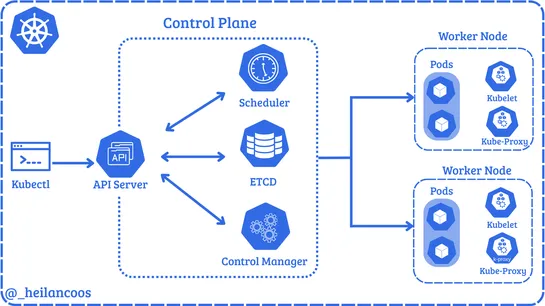
Bare metal ops aren’t what they used to be. The game’s gone full stack:API-driven provisioning,declarative workflows, andconfig convergencenow run the show. Tools likeMAAS,Foreman,Ironic, andTinkerbelltreat physical servers as programmable units. Real hardware, real APIs. Meanwhile,Kubernetes-native.. read more